You can’t possibly imagine a modern design project without a CAD (Computer-Aided Design) programme. It doesn’t matter what design you’re making: a bottle for (presumably) cold and refreshing beer, a cap for the said bottle, a plane, or a skyscraper building, you simply have to use these three tricky letters to get the job done.
But it is not enough to create and visualize the miracle of engineering of your own, you still need to get it produced to see if it actually works, and for that, you need to send your CAD files to a manufacturer. And here comes the fun part, because unless you print your magnum opus and manually hand it to a blue-collar guy to work his magic on it, you need to send it somehow.
There are tons of problems that may arise while transferring data to where it should be, but the main one is the possibility of theft, for example, due to human error, which is one of the main causes of data leaks, as various reports say. It may happen because of yourself being sloppy after thousands of hours of work and gigalitres of coffee coursing through your veins which results in your precious files being sent to the wrong address.
This might seem unlikely, but statistics indicate that in the manufacturing industry, 94% of all cyber-attacks are from industrial espionage and cyber-theft of trade secrets. The research also lists ten vulnerabilities in the CAD industry, with it being poorly composed passwords, lack of security patches, and so on, which can be shortly described as “errare humanum est”.
And how can one protect his\her CAD files and make sure that the IP will remain with the original owner?
Surely, the most obvious answer of not sharing your work with anyone is not an option as this would require you to produce everything on your own, which automatically makes your product useless by the time when (and if) you finish it.
Another pretty obvious option is to hire a team of hungry-for-blood lawyers, complete all necessary notary IP-proving procedures, and hope that it’ll work. And it probably will work unless you run into an Apple-tier team of lawyers that will rip and tear all your CAD-protection efforts leaving you behind.
But fortunately, we live in the digital era, and modern technologies make it possible to separate, protect, or manage customer data. They are difficult to port and manage, but blockchain technology can help with this very problem.
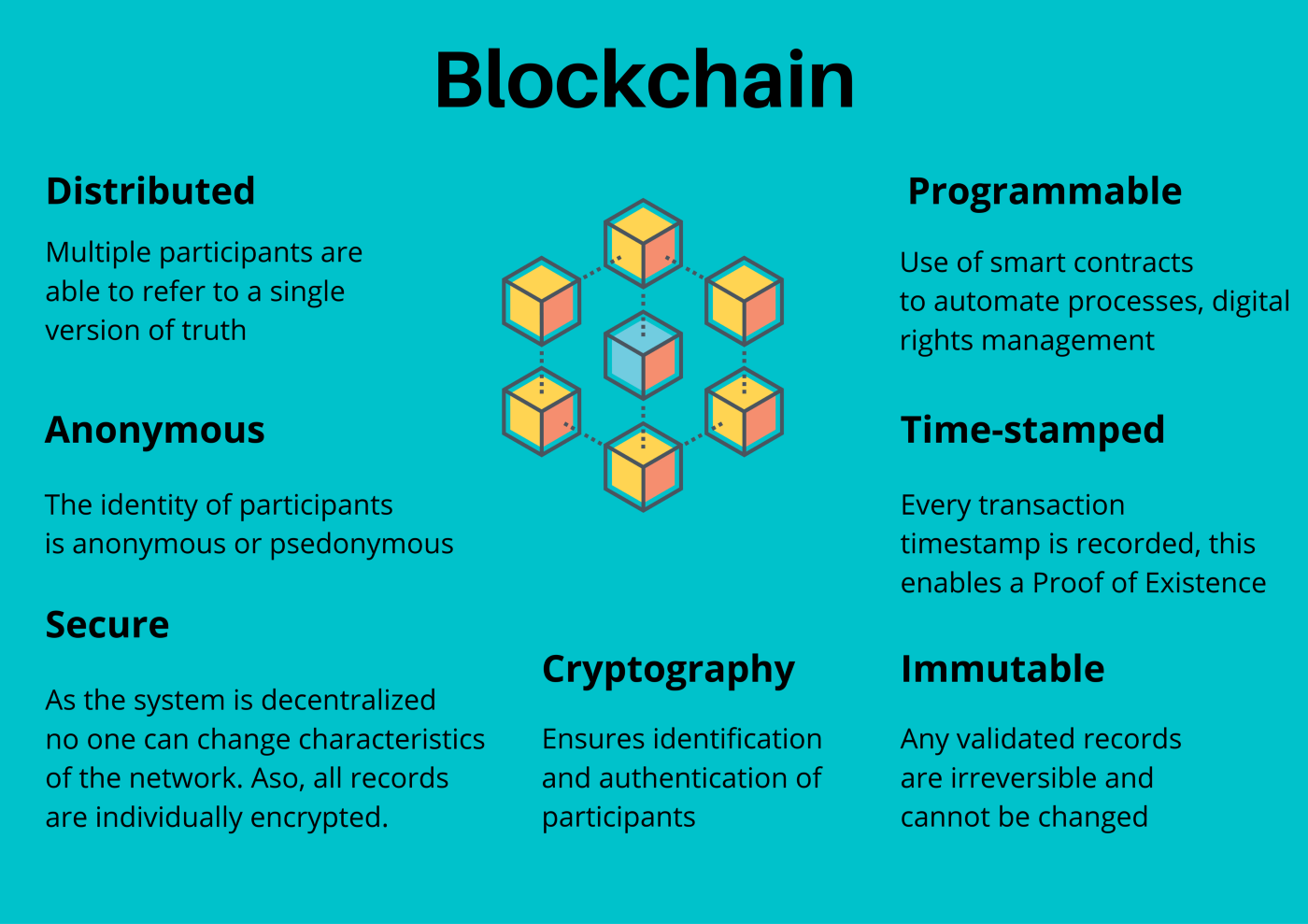
As the name suggests, a blockchain is a series of corresponding blocks of information with each and every block tied up to the rest by having a serial number inscribed on it. The trick is that the blocks store and “check” each other all the time, so in case if a hacker manages to tamper with one block, it automatically renders all the other blocks useless as there’s no verified connection between them. Plus, as was mentioned before, each block stores information about the previous one which makes the whole chain entirely traceable.
A blockchain can provide not only confidentiality but also transparency of all activities within the network. It is not a 100% solution to CAD-protection issues, but it is still mostly in development, and the situation changes all the time. So a blockchain may be viewed as the cornerstone for an ecosystem that will allow users to control access to their data, potentially having the opportunity to sell it.
So how does this CAD IP protection work?
This seems like a complicated matter, and by now, the original idea of actually printing blueprints and carrying it around might seem appealing but wait, there are several tricks up our CADChain team sleeve. They are old-fashioned in their nature but cutting-edge in the making.
One of the ways to use blockchain technology to protect CAD files is to agree on smart contracts. Said contracts are simple “if…then…” pieces of code integrated into a blockchain, and all participants execute actions only when predetermined conditions are met and agreed upon.
But the problem with smart contracts is that lawyers tend to wrap their papers into complicated terms that are hard or nearly impossible to understand for an untrained person. So to make such a contract work you need a lawyer, a programmer capable to translate it into code, and, the hardest part, this contract must be viewed by the legal system of your country as viable, with ways to mitigate the disruptive potential of bugs and problems with a receiving party that might not want to work with this kind of technology.
But we got it covered for you, as our legal department works in tandem with the software development team to create technologically advanced smart legal (digital) contracts that are legally binding, which is an unprecedented development.
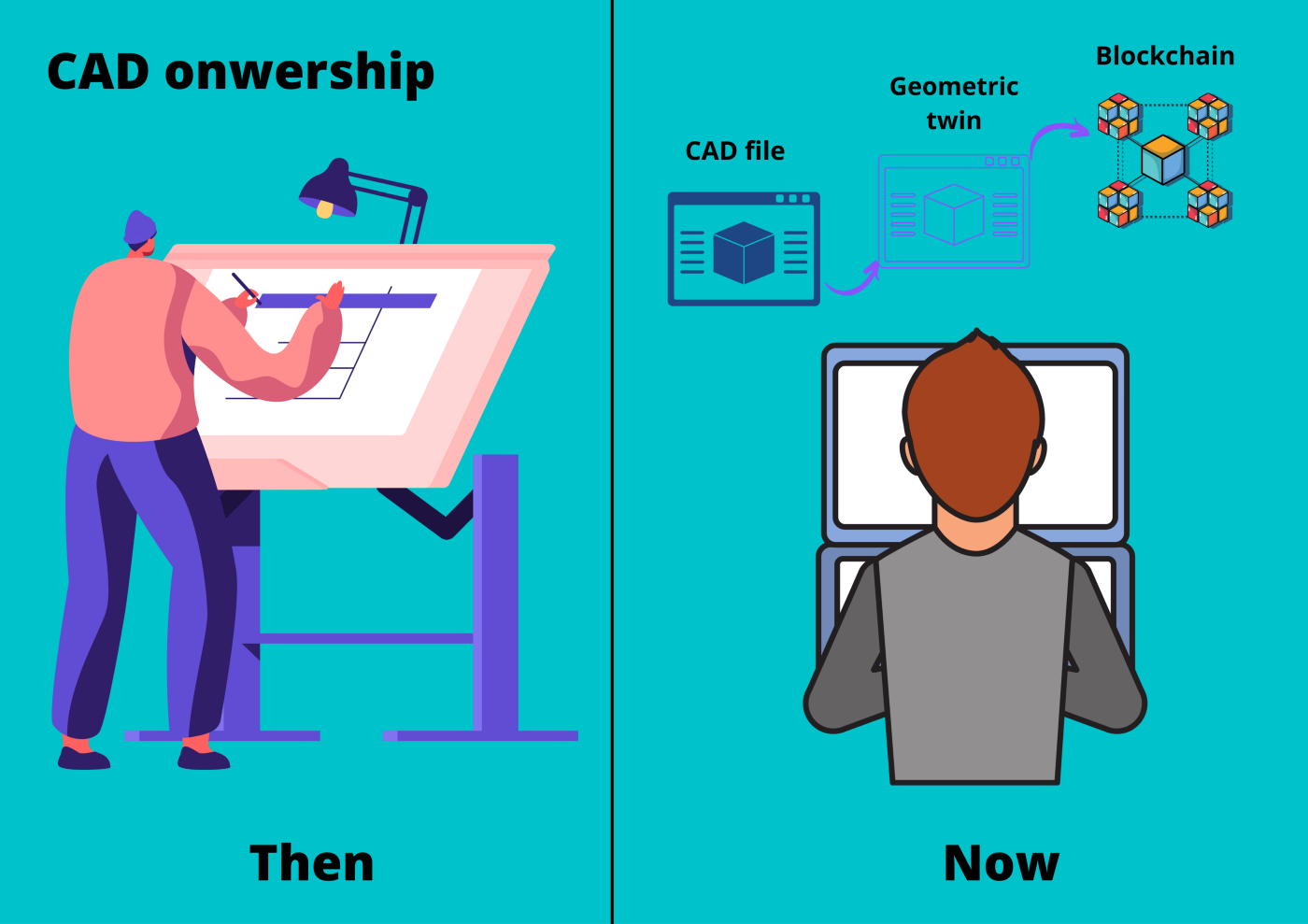
In the old days, engineers, inventors, and designers used to sign their papers by that proving the ownership.
Today, CADChain carries this idea even further, introducing BORIS, an Autodesk Inventor plugin for securing your CAD files.
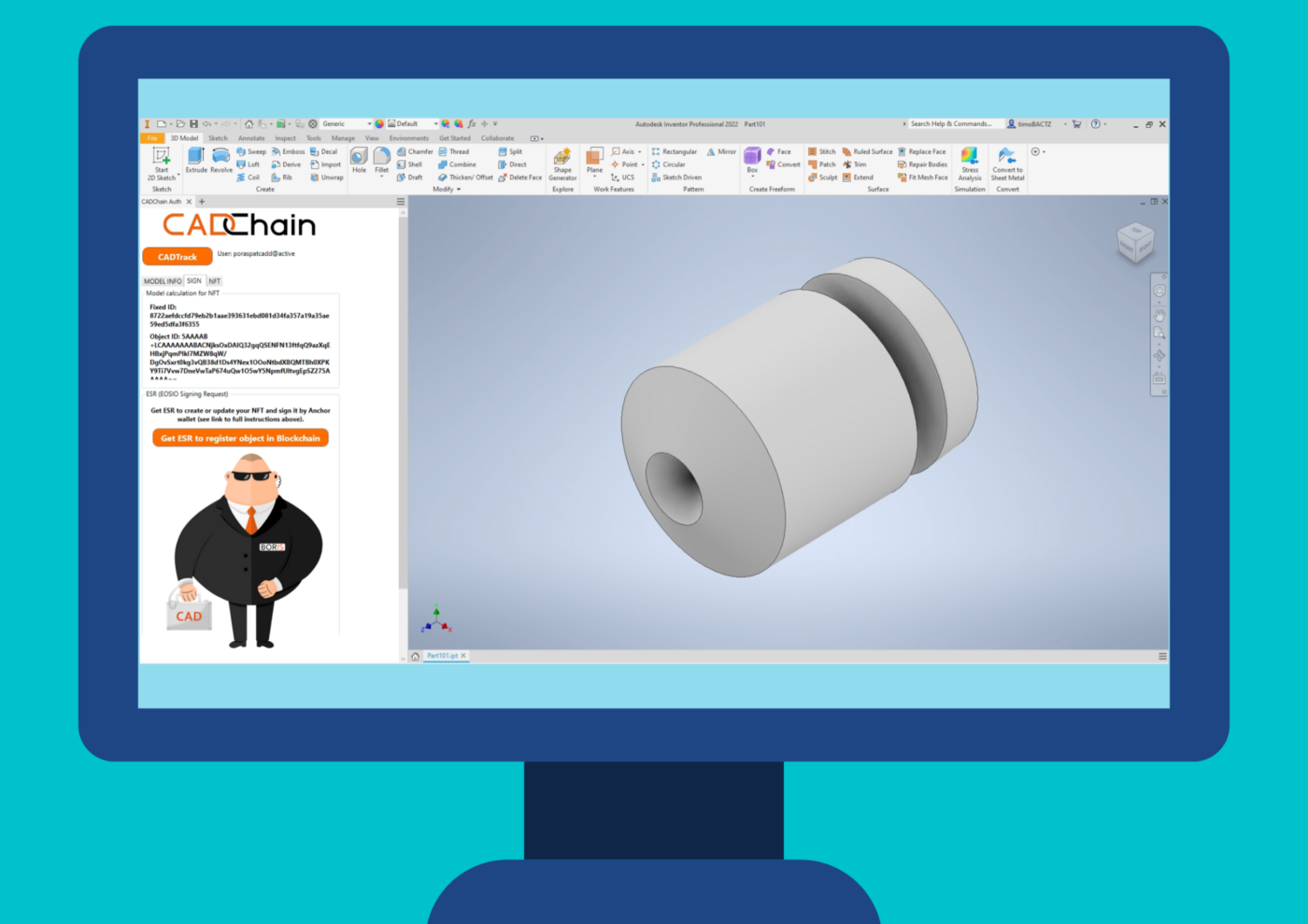
The idea is not only merely to sign your file but to create a geometric twin of the file that will serve as your own personal guardian angel that will absorb all possible damage from any sort of attacks while your original file stays secured at the repository of your choosing.
For your guardian angel not to turn into a doppelganger, there are two digital fingerprints in your possession.
One is linked to the geometric twin of your CAD file stored on the blockchain, and another one is the master key for the original files. Even if the twin is somehow leaked, you will still have a means of proving your IP ownership over your CAD files by having the said key that remains with you all the time.
So the digital fingerprint of the original file unites the CAD object ID and the owner/creator ID, which serves as timeless and immutable proof of creation and ownership.
The identity of every BORIS account is verified, ensuring certified representation and authorship. This is extremely important because the plugin ensures “first in time” registration for any intellectual asset, which automatically makes you “first in right” to IP.
This is only a small part of what BORIS is capable of to protect CAD files.
Stay tuned here to read more articles on how to protect the IP of CAD data with blockchain.


