Tesla's FSD Supervised approval in the Netherlands on April 10, 2026 is being celebrated as a triumph of AI over European regulation. And it is. But buried inside the technical details of how that approval actually happened is a story that every engineering firm and manufacturing SME in Europe should read carefully — because it reveals exactly how the most valuable data you own right now is sitting completely unprotected, and exactly how someone else can build a product from it while you watch.
I am not talking about cars. I am talking about your CAD files.
Let me explain why Tesla's regulatory battle with the RDW is one of the most relevant technical case studies for engineering IP protection in 2026, and what you can do about it today.
TL;DR: Tesla FSD Just Proved Your Engineering IP Is One Shared File Away From Being Someone Else's Product
Tesla's FSD approval required proof that its AI-generated driving behavior could be traced back to specific training data, tested on specific road conditions, and verified as distinct from any other country's software version. The RDW explicitly confirmed the European and US versions are not comparable — they are separate, documented, traceable builds. That level of data provenance is precisely what most engineering SMEs do not have for their CAD files. When a design partner, manufacturer, or competitor ships a product that looks suspiciously similar to yours, you need the same thing Tesla needed: a timestamped, immutable, jurisdictionally-specific evidence trail. This article breaks down what that means technically and how to build it.
What the RDW Actually Demanded From Tesla — and Why It Matters for CAD Data
The Dutch vehicle authority RDW spent more than 18 months testing FSD Supervised on its own closed test track and on Dutch public roads before issuing type approval on April 10, 2026. The approval is classified under UN R-171, the UNECE regulation for Driver Control Assistance Systems (DCAS).
Here is the technical requirement that gets almost no coverage in the mainstream automotive press: the RDW did not accept Tesla's US data as evidence. The authority explicitly stated in its approval documentation that the European software version "differs substantially" from the US version and that the two are "therefore not comparable one-to-one." Tesla had to demonstrate, through 1.6 million kilometers of EU-specific road testing, that the Dutch version of FSD was a distinct, documented, auditable build — not a copy of something already deployed elsewhere.
This is a data provenance requirement. The regulator needed to know: what exact data trained this system, on what roads, under what conditions, producing what measurable outcomes. Without that chain of evidence, no approval.
Now apply that logic to your engineering IP.
When you share a CAD file with a contract manufacturer in Poland, a design partner in Germany, or a 3D printing bureau in Portugal, what is your evidence that the file you sent is the original, that it was yours to send, and that the version they used is the version you authorized? Most engineering SMEs have nothing. A shared folder timestamp. An email thread. Maybe a PDF export.
That is not a chain of evidence. That is a story you tell yourself.
The Technical Gap: Why Standard CAD File Security Fails
Most engineering teams use one of three approaches to protect their design data, and all three have the same fundamental flaw.
Approach 1: Access control in cloud storage. OneDrive, Box, SharePoint, and similar platforms restrict who can open a file. But once a file is downloaded, it leaves the protected environment entirely. There is no tracking, no audit trail, and no mechanism to know what happened to the file after it was accessed. A contractor opens your STEP file, saves a copy locally, and shares it with their manufacturer. You have no record of any of this.
Approach 2: Non-disclosure agreements. NDAs are legal instruments, not technical ones. Enforcing an NDA requires proving that the protected information was disclosed without authorization. To prove that, you need evidence of what information was in the file, when it was created, who had access, and when the breach occurred. Without that evidence, your NDA is a strongly worded document with no technical backing.
Approach 3: Traditional patents. Getting a patent in Europe can take several years and cost tens of thousands of euros. Patents protect a disclosed invention — which means publishing the very information you were trying to protect. And patents are territorial, meaning the protection you register in the Netherlands does not automatically cover China, where your design may be copied and manufactured at scale.
All three approaches share the same gap: they protect against known threats in known jurisdictions, using evidence that must be assembled after the fact. Tesla's RDW submission worked because the evidence was built into the system from the beginning, not assembled after something went wrong.
What Tesla's Evidence Architecture Actually Looked Like
Let's get technical about what Tesla submitted to the RDW, because this is the model for how engineering IP evidence should be structured.
Tesla's FSD system generates continuous telemetry from 8 cameras providing 360-degree coverage, processed through 48 distinct neural networks that together output approximately 1,000 distinct tensors (predictions) per timestep. A full training build of FSD neural networks requires 70,000 GPU hours and processes over 1.5 petabytes of driving data. Every kilometer driven by a Tesla vehicle with FSD active contributes to a versioned, timestamped data record.
The specific build deployed in the Netherlands is FSD v14.2.2.5, delivered through software update 2026.3.6. This is not the same as FSD v14.3 running in North America. The two builds have different training data, different behavioral tuning, and different regulatory documentation. The RDW tested v14.2.2.5 specifically — not the product category, not the general technology, but that exact version against those exact Dutch road conditions.
This is version-controlled, jurisdiction-specific, auditable evidence. Each version has a unique identifier. Each deployment has a traceable update record. Each safety-critical incident must be reported to the RDW no less than annually.
Now compare this to how most engineering SMEs version their CAD files.
A file named housing_v3_FINAL_revised_FINAL2.SLDPRT in a shared folder with no blockchain record, no geometric fingerprint, no timestamped ownership registration, and no automated access log. If that design appears in a competitor's product eighteen months from now, you have a version name and an email thread. Tesla had 1.6 million kilometers of traceable, jurisdiction-specific test data. Guess whose IP dispute goes better in court.
The Geometry-Cryptography Link: How CADChain Solves What Access Control Cannot
At CADChain, we built our solution specifically around the evidence gap that traditional security approaches leave open. The technical architecture is worth explaining, because it mirrors the same principle Tesla demonstrated to the RDW: make the evidence inseparable from the data itself.
Here is how our BORIS plugin works for Autodesk Inventor, SolidWorks, and Blender.
Step 1: Geometric twin creation. When a designer registers a CAD file through the BORIS plugin, the system analyzes the geometry of the 3D model and creates a geometric twin — a mathematical representation of the model's unique spatial properties. This is not a copy of the file. It is a set of geometric measurements that uniquely identify this specific design, similar to how a fingerprint identifies a person without storing their full DNA.
Step 2: Cryptographic hashing. The geometric data is hashed using cryptographic functions that produce a fixed-length output unique to that geometric configuration. Any change to the model — adding a fillet, modifying a bore dimension, adjusting a wall thickness — produces a completely different hash. This makes it mathematically impossible to claim that an altered design is "the same" as the registered original.
Step 3: Blockchain registration. The hash, combined with the verified identity of the file owner, is written to our GDPR-compliant blockchain protocol. The entry is timestamped, immutable, and permanent. No central authority can alter it. No one — including CADChain — can access the underlying CAD file. We store the fingerprint, not the design.
Step 4: Verifiable certificate generation. The registration produces a shareable blockchain certificate, available as a verifiable web link or a tamper-evident PDF. The certificate shows the date of creation, the owner identity, and the cryptographic proof that this specific geometric configuration was registered at this specific time. In an IP dispute, this certificate serves as "first in time, first in right" proof of ownership — the same principle that makes blockchain timestamps legally admissible in an increasing number of European jurisdictions.
The result is a chain of evidence that is built before anything goes wrong, not assembled after a dispute starts.
The Ricardian Contract Layer: Licensing That Enforces Itself
Access control tells you who opened a file. A Ricardian contract tells you what they were authorized to do with it — and enforces those terms automatically.
Ricardian contracts are legal agreements that are both human-readable and machine-executable. Unlike traditional smart contracts, which require specialized programmers to write and specialized lawyers to interpret, Ricardian contracts sit at the intersection of plain-language legal terms and executable code. When a designer shares a CAD file through the BORIS system, the sharing event can be governed by a Ricardian contract that specifies:
- Who is authorized to view the file
- Whether they can modify it
- Whether they can share it further
- The duration of their access license
- What jurisdiction's law governs the agreement
- Automatic termination conditions
When the contract terms expire or are violated, access is revoked. There is no need to call a lawyer, send a cease-and-desist, or start an evidence-gathering process. The violation is recorded on the blockchain, timestamped, and the access is terminated at the technical level.
Compare this to how most engineering firms handle design licensing: a PDF agreement signed by email, stored in someone's inbox, with no technical enforcement mechanism and no automatic audit trail. The contract is a statement of intent. The Ricardian contract is a statement of intent with a technical enforcement layer.
The GDPR Angle Tesla Had to Navigate — and Why It Directly Applies to Your CAD Data
One of the less-discussed aspects of Tesla's RDW approval is the data protection dimension. FSD generates continuous video and sensor data from the vehicle's cameras and systems. Under EU GDPR and related data protection frameworks, Tesla must address: how video data is stored, processed, and anonymized; whether cross-border data transfers to US servers comply with EU data transfer rules; and what controls owners have over data collection and consent. These requirements were part of the behind-the-scenes regulatory negotiation, and they add to the compliance overhead that any company deploying AI on EU roads must manage.
Your CAD data faces a parallel compliance structure, and most engineering SMEs do not know it.
Under GDPR Article 5, personal data must be processed with integrity and confidentiality. If your CAD files contain data that can be linked to individuals — and in bespoke manufacturing, client-specific designs often can — then how you store, share, and track those files is a GDPR matter, not just an IP matter. A breach of that data is not just a commercial loss; it is a potential regulatory violation with fines up to 4% of annual global turnover under GDPR Article 83.
The blockchain protocol underlying BORIS is built with GDPR compliance from the ground up. The system stores geometric fingerprints and access metadata on the blockchain, not the CAD files themselves. The files stay wherever you choose to store them — your own server, your PLM system, your cloud environment. CADChain has no access to the underlying design data. This architecture separates the evidentiary layer (what blockchain needs: proof of ownership and access events) from the data layer (what GDPR governs: the actual design content).
This is not an accident of design. It is the only architecture that satisfies both IP protection requirements and GDPR simultaneously — which is why the European Commission has verified blockchain-based data tracking as a legitimate approach for these use cases.
The 3D Printing Vulnerability That Tesla's Approval Indirectly Exposed
Tesla's FSD approval creates a specific IP risk for engineering SMEs that is moving faster than most firms recognize.
FSD requires precise mapping data, geometric sensor inputs, and object recognition for real-world 3D environments. The technology underpinning FSD — deep neural networks trained on geometric data — is the same class of technology now being deployed in reverse-engineering tools that can reconstruct CAD models from physical products, scanned objects, or even from images.
A 3D scanner costing under €5,000 can now produce a printable CAD file from a physical component in under an hour. An AI-assisted reverse-engineering tool can turn that scan into a parametric model suitable for modification and re-manufacture. The design protection lifecycle that used to run years — the time between your product launch and a competitor's first physical copy — has compressed to weeks in some manufacturing categories.
CADChain has a proposition specifically for 3D printing protection currently in stealth mode, because the gap in 3D printing IP law is real and growing. The European Commission has published multiple papers on IP protection for 3D printing, acknowledging that copyright, patent, and design rights do not cleanly map to digital design files and their physical outputs. The current legal framework was written before additive manufacturing became an accessible industrial process.
The parallel to Tesla's regulatory situation is exact: the rules were written for a technology that preceded the product. Just as Tesla had to use EU Article 39 exemptions because FSD did not fit existing UNECE categories, engineering SMEs trying to protect 3D-printable designs find that existing IP law was written for a world where manufacturing required specialized machinery and significant capital. That world is gone.
Evidence Architecture: A Technical Comparison
How does blockchain-based CAD IP protection compare to the alternatives currently used by engineering SMEs? Here is the technical breakdown.
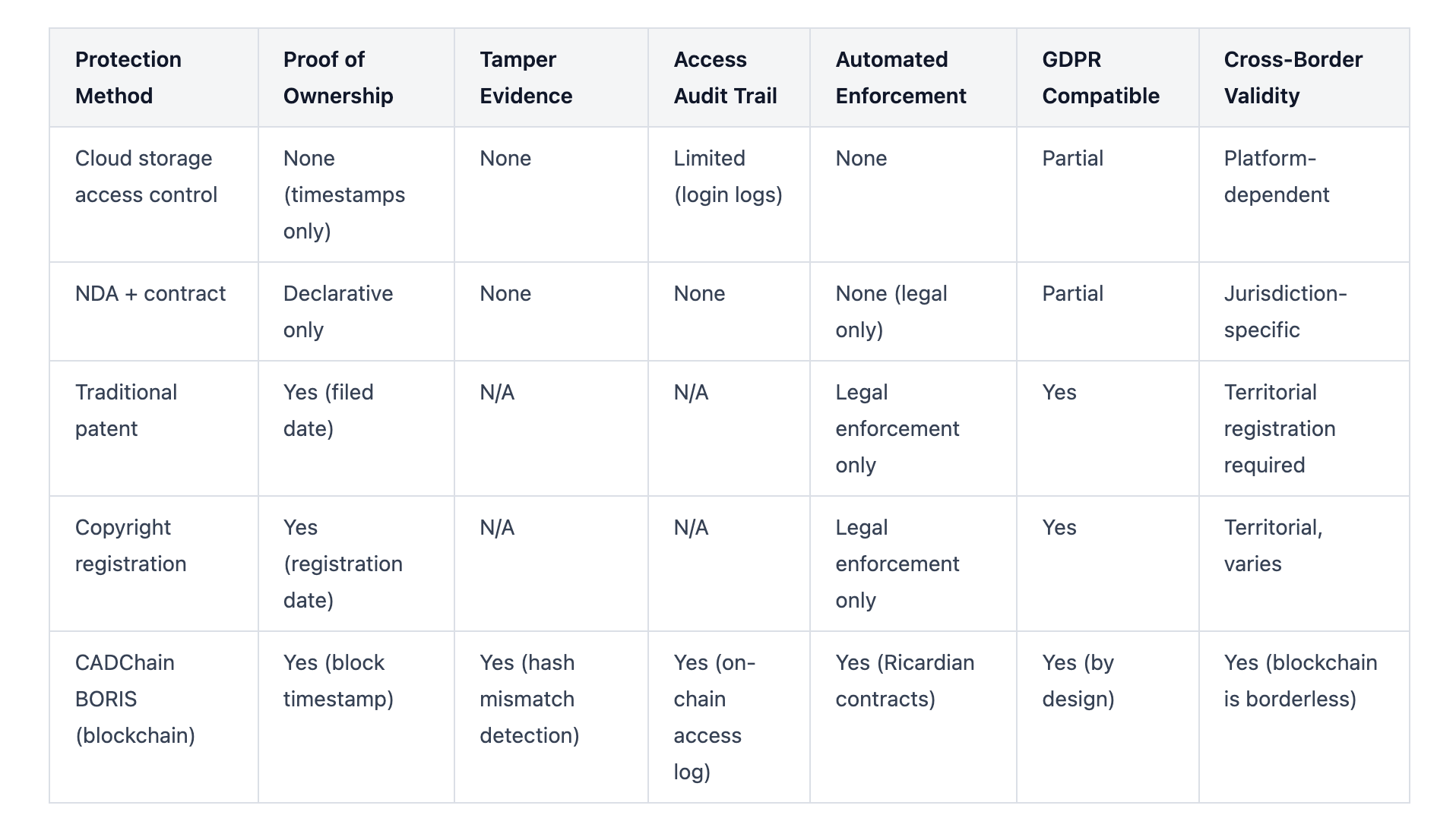
The critical column for most engineering SMEs is "Cross-Border Validity." A patent registered in the Netherlands does not protect your design in Vietnam, where your component may be manufactured and shipped globally. A blockchain timestamp is not a jurisdiction. It is a mathematical fact recorded on a distributed ledger that any court in any country can verify independently.
The World Intellectual Property Organization has acknowledged blockchain-based IP registration through its WIPO PROOF initiative, which specifically addresses the needs of holders of unregistered rights — the category that covers most CAD-based engineering IP, which is held as a trade secret rather than a patent.
The Over-the-Air Update Problem: What Engineering Firms Miss About Design Iteration
Tesla's FSD system receives over-the-air (OTA) software updates continuously. Each update is a versioned release with a specific build number. The RDW is notified of significant changes and can require additional review. This means that every material change to the system generates a new version record with a new timestamp and a new traceable chain of evidence.
FSD v14.3, released just days before the Netherlands approval, rewrote the AI compiler and runtime using MLIR (Multi-Level Intermediate Representation), delivering 20% faster reaction times according to Tesla's internal benchmarks. This is a major architectural change. Tesla's version control records it as a distinct build, separate from the v14.2.2.5 deployed in the Netherlands. Both exist simultaneously, both are traceable, and neither can be confused with the other in a regulatory or liability context.
Engineering designs evolve the same way. A component goes through ten revisions before manufacturing. The revision that ends up in the product may be revision 7. If a dispute arises about whether your design or a competitor's came first, which revision do you prove? Can you demonstrate that revision 7 existed before revision 1 of the competing design?
BORIS handles this through a concept we call continuous registration. Each time a design file is saved through the BORIS plugin, the system generates a new geometric twin and hash, creating a versioned blockchain record of that design state. The result is a full development history on-chain: a timestamped record of every material iteration, who made it, and when.
If a dispute arises, you can demonstrate not just that you own the final design, but that you developed it incrementally over a specific period, with specific intermediate states, by specific individuals within your organization. That is the engineering equivalent of Tesla's 1.6 million kilometers of EU-specific test data: evidence built into the process, not assembled after the fact.
SOP: How to Build a Tesla-Grade IP Evidence Architecture for Your Engineering Firm
Here is the exact process for implementing blockchain-based CAD IP protection that generates defensible evidence as a by-product of your normal design workflow.
Step 1: Audit your current evidence gaps. List every external party that receives your CAD files in any format: contract manufacturers, design partners, certification bodies, clients, 3D printing services. For each, document what access control you currently have, what your audit trail shows, and what evidence you could produce today if a file appeared in a competitor's product. Most firms find they can produce email confirmations and folder timestamps — nothing more.
Step 2: Install the BORIS plugin for your CAD platform. BORIS is available for Autodesk Inventor, SolidWorks, and Blender. Installation runs inside your existing CAD environment. No workflow change is required at the point of design. The protection layer operates as you work.
Step 3: Register your existing design library. Start with your highest-value designs — the ones with the most commercial exposure or the longest development history. Each registration takes seconds from within the CAD software. The system creates the geometric twin, hashes it, and writes the ownership record to the blockchain. You receive a verifiable certificate immediately.
Step 4: Set up Ricardian contract templates for your sharing workflows. Define the standard terms under which you share designs with each category of external party. Manufacturers get different terms from design partners. Certification bodies get read-only access with no redistribution rights. Clients get licenses scoped to their specific use case. Set these templates once; the system applies them automatically when you share files.
Step 5: Enable continuous registration for active projects. For designs currently in development, turn on BORIS continuous registration. Every saved version becomes a timestamped blockchain record. Your development history builds automatically.
Step 6: Generate certificates before each major sharing event. Before sending a design to a new external party, generate a fresh blockchain certificate. This creates a "before" record: proof that the specific design existed in your possession, in its current state, on this date, before it was shared. If the design appears elsewhere later, you have a timestamped record predating that appearance.
Step 7: Report incidents to the blockchain immediately. If you discover a potential IP violation, the timestamp at which you documented the suspected violation matters legally. Write a record to your blockchain audit trail noting what you observed and when. This is the digital equivalent of a notarized letter — timestamped, immutable, and verifiable.
What Tesla's Approach to Chinese Competition Tells Engineering SMEs
Tesla's approval in the Netherlands came with an explicit warning from analysts: Xpeng and BYD are pursuing their own European supervised autonomy approvals under the same UNECE framework. If the European Commission opens the door through majority vote, it opens it for Chinese competitors too. Tesla will not hold exclusive European autonomous driving access for long.
The same dynamic operates in manufacturing. Chinese manufacturers with access to your CAD files — through a supply chain partner, a shared component supplier, or a direct reverse-engineering operation — can move from your design to a competing product faster than at any previous point in manufacturing history. The cost of precision CNC machining has dropped 60% over the past decade. 3D printing of metals, polymers, and composites at industrial quality is now accessible to contract manufacturers with entry-level capital.
The barrier to copying your product used to be manufacturing capability. That barrier is largely gone. The remaining barrier is evidence: your ability to demonstrate in court, quickly and cheaply, that your design came first and that its appearance in a competitor's product is traceable to a specific breach of a specific sharing event.
CADChain's digital fingerprinting technology creates that evidence automatically, as part of your design workflow. It does not change how you design. It changes what you can prove after the design is done.
The Industrial Design Data Regulation Coming That Nobody Is Preparing For
Tesla's approval created reporting obligations. The RDW requires Tesla to submit safety-critical incident reports at minimum annually, along with ongoing performance data. This is a regulatory compliance burden that Tesla built its systems to handle from day one.
The EU's AI Act, which entered enforcement phases in 2025 and 2026, creates parallel compliance obligations for any company using AI systems in product design, quality control, or manufacturing decisions. Engineering firms using AI-assisted CAD tools, generative design platforms, or machine-learning-based quality inspection are already subject to these requirements in many cases — and most do not know it.
On top of the AI Act, the EU's proposed Data Act and the Platform-to-Business regulation create obligations around how manufacturing data, including design files, is shared across supply chains. These obligations will require firms to demonstrate what data they hold, where it came from, how it was used, and what access controls governed its use.
Blockchain-based design registration positions your firm to answer these questions automatically. Every registration creates an auditable record. Every sharing event through the Ricardian contract system creates a traceable log. When a regulator or auditor asks "when did this design enter your system, and who had access to it," your answer is not a spreadsheet reconstructed from email threads. It is a cryptographically verifiable blockchain record.
Mistakes Engineering SMEs Make With CAD IP Protection
Mistake 1: Treating IP protection as a legal problem rather than a technical one. Your lawyer can write the contract. Only a technical system can generate the evidence the contract requires to be enforced.
Mistake 2: Protecting the file but not the design. Encrypting a file protects it while it is encrypted. Once decrypted and opened by your manufacturer, it is as unprotected as it ever was. The geometric fingerprint approach protects the design itself — the specific configuration of geometry that represents your IP — regardless of what container it is stored in.
Mistake 3: Registering IP only after something goes wrong. Tesla did not build its evidence file after the Netherlands asked for it. It built it over 18 months of testing, as a continuous by-product of operating the system. Your IP evidence needs to predate the threat, not respond to it.
Mistake 4: Assuming your NDA covers your liability. An NDA establishes an obligation. Proving a breach of that obligation requires evidence of what was protected, when, and what happened to it. Without the technical evidence layer, your NDA is a statement of good intentions.
Mistake 5: Not versioning your design history on-chain. The design you prove you own is the design as it existed at a specific point in time. If you registered only the final version, you have proof of one moment. If you registered continuously through development, you have proof of the entire creative process — which is far more powerful in a dispute over originality.
Mistake 6: Sharing files in format-neutral containers. Sending a STEP file or STL export to a manufacturer removes most of the metadata from the original parametric CAD model. It also removes your ability to trace what specific version of your design was shared. Always share through a system that generates a sharing record linked to a specific registered version.
FAQ
How does blockchain IP protection for CAD files actually work technically?
Blockchain IP protection for CAD files works through a three-layer process. First, the system creates a geometric twin of the CAD model — a mathematical representation of its unique spatial properties derived from the actual 3D geometry. Second, this geometric data is cryptographically hashed to produce a unique fixed-length string that acts as a digital fingerprint for that specific design configuration. Any modification to the model, however minor, produces a completely different hash. Third, the hash and the verified identity of the file owner are written as a permanent, timestamped entry to a distributed blockchain ledger. The blockchain entry cannot be altered, back-dated, or deleted by any party, including the platform provider. This creates an immutable "first in time" ownership record. CADChain's BORIS plugin performs all three steps from within Autodesk Inventor, SolidWorks, or Blender, generating a verifiable blockchain certificate as proof of registration.
What is the legal standing of a blockchain certificate for CAD IP in European courts?
Blockchain timestamps are increasingly accepted as evidence of prior creation in European IP litigation. The World Intellectual Property Organization has explicitly acknowledged blockchain-based IP registration through its WIPO PROOF initiative, which targets holders of unregistered rights — the most common situation for CAD-based engineering IP held as trade secrets. In the Netherlands, Germany, and other EU member states, courts accept digital evidence under the same rules governing electronic documents, with authenticity determined by the cryptographic integrity of the record. A blockchain certificate cannot be forged: its validity is verifiable by any party using the public ledger, without access to the underlying design data. The evidentiary strength of a blockchain certificate is significantly higher than a folder timestamp or an email chain, which can be modified or fabricated. Firms should note that blockchain evidence strengthens but does not replace legal IP strategy — consulting a specialist in digital IP law alongside technical protection is advisable.
Does CADChain access my CAD files when I use BORIS?
No. CADChain has no access to your CAD files at any point during the registration or tracking process. The BORIS plugin creates a geometric twin — a mathematical fingerprint derived from the 3D geometry — and sends only that fingerprint and your verified ownership identity to the blockchain. The actual CAD files remain wherever you choose to store them: your own server, your company's PLM system, your cloud storage, or your local machine. This architecture satisfies GDPR requirements because no personal or commercially sensitive data from the design is transferred to or stored by CADChain. The blockchain receives a cryptographic hash (a one-way transformation with no reverse) and metadata about the registration event. The underlying design cannot be reconstructed from this data.
How does CADChain's BORIS differ from simply using a file hash or a versioning system in my PLM?
A standard file hash confirms whether a file has changed. It does not establish who created it, when it was first created, or who had authorized access to it at any given time. A PLM versioning system records your internal design history within your own system — but that record is controlled by you and can be modified by anyone with administrator access. Neither approach creates a third-party verifiable, tamper-proof ownership record that an external party (a court, a regulator, or a client) can independently verify without trusting your word. CADChain's blockchain registration creates exactly that: a verifiable, immutable, timestamped record maintained on a distributed ledger that no single party controls. The geometric twin approach also adds a layer that file hashing misses: it captures the design's spatial identity, not just the file's binary state. This means that even if a design is exported to a different file format (STEP, STL, IGES), re-imported, and modified slightly, the geometric fingerprint comparison can detect the relationship between the registered original and the suspected copy.
What CAD platforms does BORIS currently support?
BORIS is currently available for Autodesk Inventor (in public beta), Blender (in alpha as BlendedBoris), and SolidWorks. A plugin for Autodesk Fusion 360 is also available. A proposition for 3D printing specific protection is in stealth mode. Each platform integration is built as a native plugin that operates within the existing CAD environment — designers do not need to export files to a separate tool or change their standard workflow. The registration process runs in the background while the designer works, generating blockchain records linked to specific save events without interrupting the design process. Development of additional platform integrations is ongoing. If your primary CAD environment is not yet listed, contact CADChain directly — the geometric twin and hashing architecture is platform-agnostic at the core level.
How does a Ricardian contract differ from a standard NDA for protecting shared CAD files?
A standard NDA is a legal instrument: it establishes obligations but has no technical enforcement mechanism. Proving a breach requires evidence gathering, legal proceedings, and often expensive discovery processes. A Ricardian contract is both a legal document and an executable program: its terms are written in human-readable language and simultaneously encoded as machine-executable conditions linked to access permissions on the blockchain. When a file is shared through CADChain's system with a Ricardian contract governing the sharing event, the contract terms are enforced technically — access to the file is revoked automatically when contract conditions expire or are violated, and the violation is recorded as an immutable event on the blockchain. This creates an evidence trail of the breach at the moment it occurs, not weeks later when you discover it. The Ricardian contract handles automated licensing (including time-limited access for specific project durations), NDA terms, redistribution restrictions, and jurisdiction specification — all with technical enforcement and automatic audit logging.
What does the EU AI Act mean for engineering firms using AI-assisted CAD tools?
The EU AI Act, which moved into enforcement phases from 2025 onward, classifies AI systems by risk level and imposes compliance obligations accordingly. AI systems used in product safety-related applications — which includes any AI-assisted design tool influencing products that could pose physical risks — may fall into higher-risk categories requiring documentation of training data provenance, system validation records, and human oversight mechanisms. Engineering firms using AI-assisted generative design, topology optimization, or quality inspection tools should audit whether these tools fall under AI Act scope, and what documentation obligations apply. Separately, the proposed EU Data Act will create obligations around how manufacturing and design data is shared across supply chains — including requirements to demonstrate what data you hold and under what access conditions. Blockchain-based design registration directly addresses both requirements: it creates auditable provenance records for design data and documented access logs for sharing events. Firms that implement this now will be ahead of compliance obligations that will become mandatory for larger supply chain partners within the next two to three years.
Can blockchain IP protection help if a design is copied and manufactured in a non-EU country?
Blockchain timestamps are not jurisdiction-specific — the ledger record exists on a distributed network accessible globally and verifiable by any court that accepts digital evidence. In practice, enforcing IP rights in manufacturing jurisdictions like China, Vietnam, or India still requires navigating those countries' specific legal systems, which varies significantly. What blockchain protection gives you globally is the strongest possible "first in time" evidence: a verifiable record, dated before the alleged copying occurred, that cannot be disputed on grounds of fabrication or modification. This is particularly valuable in jurisdictions that use the "first to file" principle for IP rights, where having a pre-dated blockchain registration can establish your prior claim even without a registered patent. Combined with WIPO's international IP registration mechanisms, blockchain-based prior creation evidence strengthens your position in any jurisdiction compared to folder timestamps or email chains. It does not eliminate the complexity of international IP enforcement, but it gives you the strongest technical foundation for any enforcement action.
How does CADChain's approach compare to simply registering a patent for engineering IP?
Patents and blockchain IP protection serve different purposes and are most effective in combination. A patent grants exclusive rights to a disclosed invention for a fixed term (typically 20 years) in the specific territories where it is registered. It requires public disclosure of the protected technology, costs tens of thousands of euros to file and maintain across multiple territories, and takes several years to grant. During the application period, the design is not yet protected, only pending. Blockchain registration through BORIS takes seconds, costs a fraction of patent filing fees, and produces immediate, verifiable proof of creation and ownership without any disclosure of the protected design. It protects trade secrets (the most common form of engineering IP protection) rather than inventions. The two approaches are complementary: blockchain registration provides immediate, ongoing protection for all design iterations and trade secrets, while patent filing provides formal exclusivity for your most commercially significant final designs. Many CADChain users use BORIS to protect the development history and intermediate design states that are not patentable, while filing patents only for the specific innovations that justify the cost and disclosure.
What is the pricing model for CADChain's BORIS, and is it accessible for small engineering firms?
CADChain operates as a B2B SaaS with pricing designed to be accessible to European engineering SMEs. The model includes tiered pricing based on team size and feature requirements, with options ranging from small team access up to enterprise licensing for larger organizations. The CADChain resources hub notes that blockchain IP protection costs range from accessible entry-level options for startups to enterprise licenses, with most solutions offering tiered pricing based on team size and usage volume. Given that the average cost of an IP dispute in Europe runs to hundreds of thousands of euros in legal fees alone — before any damages calculation — the cost of prevention is orders of magnitude lower than the cost of litigation. For a bootstrapped engineering SME, the calculus is straightforward: one prevented IP dispute pays for years of blockchain IP protection. Contact CADChain directly at team@cadchain.com for current pricing and to arrange a demo specific to your CAD platform and workflow.
Your Design Submitted Documentation. What Does Yours Show?
Tesla spent 18 months building an evidence file that the RDW could not reject. Every kilometer of testing contributed to a traceable, versioned, jurisdictionally-specific record of what the system did and when it did it. The approval came because the evidence was built into the process from the beginning.
Your CAD files are generating evidence right now. The question is whether that evidence is being captured in a form that protects you — or whether it is sitting in a shared folder, undocumented and unprotected, waiting for someone else to claim it.
BORIS creates that evidence automatically, from within the CAD tools your engineers already use. No workflow change. No disruption. Just a tamper-proof audit trail building in the background while your team designs.


